Vulta Intelligence Launches as Credential Lookup Service With 14.2 Billion Indexed Records, Telegram Bot, and Pay-Per-Query ULP Extraction
Quick Facts
Incident Overview
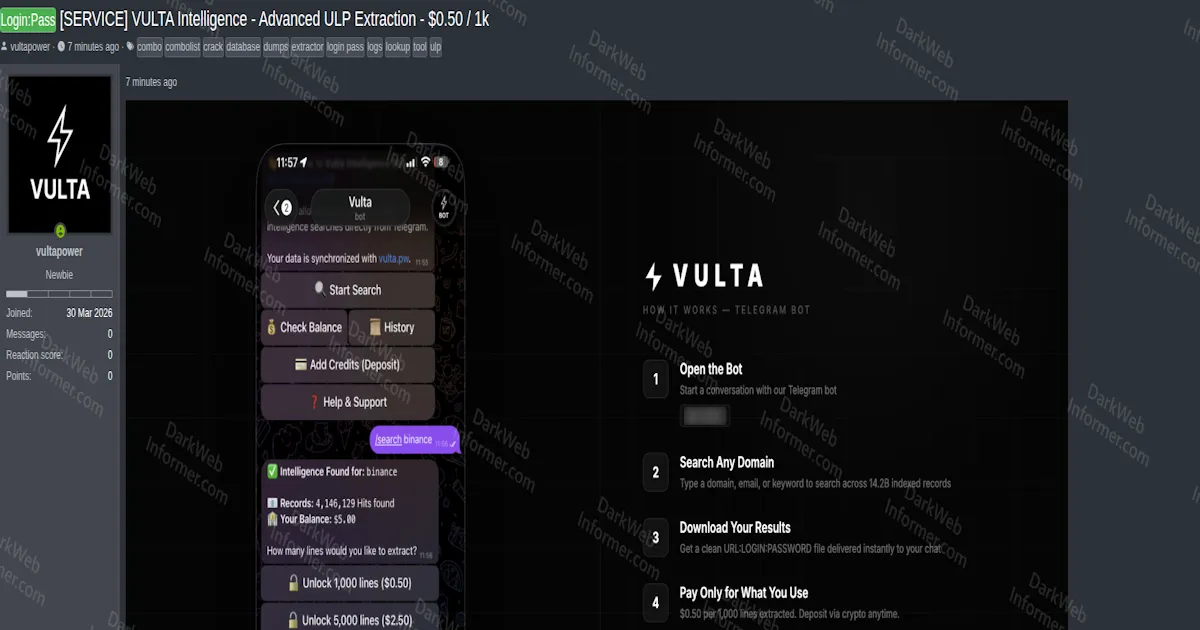
A threat actor going by vultapower has launched Vulta Intelligence, a credential lookup and extraction service that claims to index 14.2 billion records in URL:Login:Password (ULP) format. The service is accessible through both a Telegram bot and a web dashboard at vulta.pw, with real-time synchronization between the two interfaces. It's marketed as a tool for searching domains, emails, or keywords against massive databases of stolen credentials sourced from infostealer logs and combolists.
The service works in a straightforward four-step process:
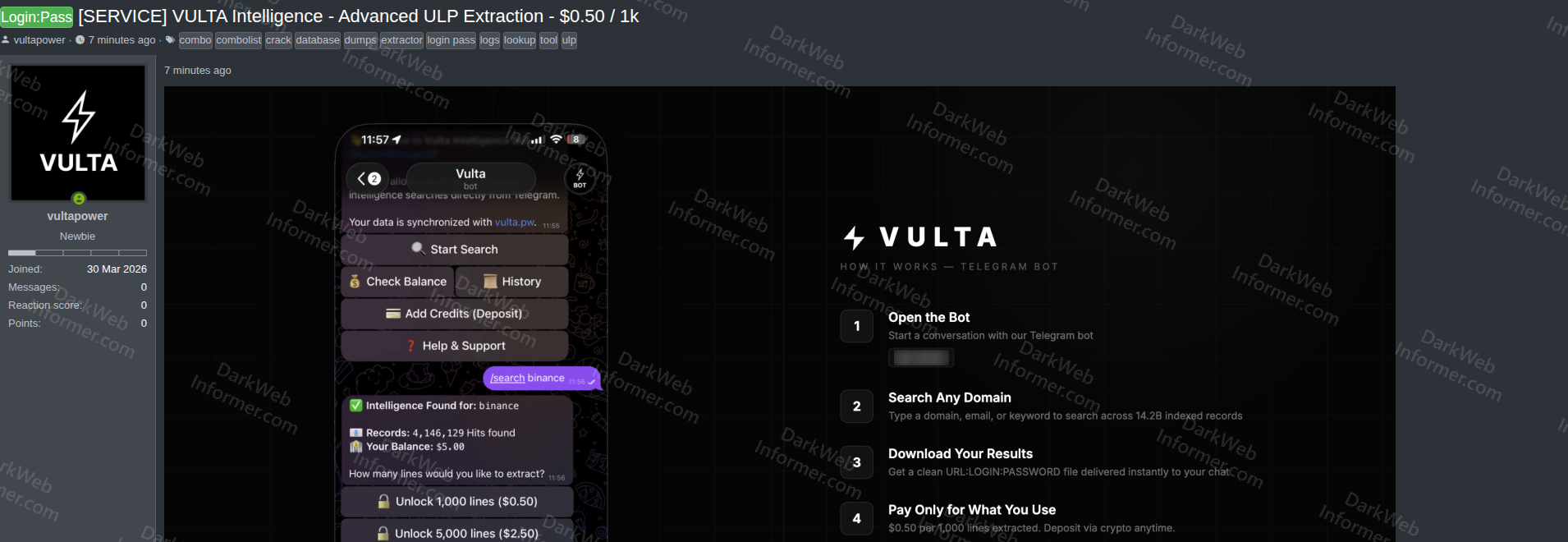
- Search: Users type a domain, email address, or keyword into the Telegram bot or web interface. The demo screenshot shows a search for "binance" returning 4,146,129 hits.
- Results: The system returns a hit count and asks how many lines the user wants to extract.
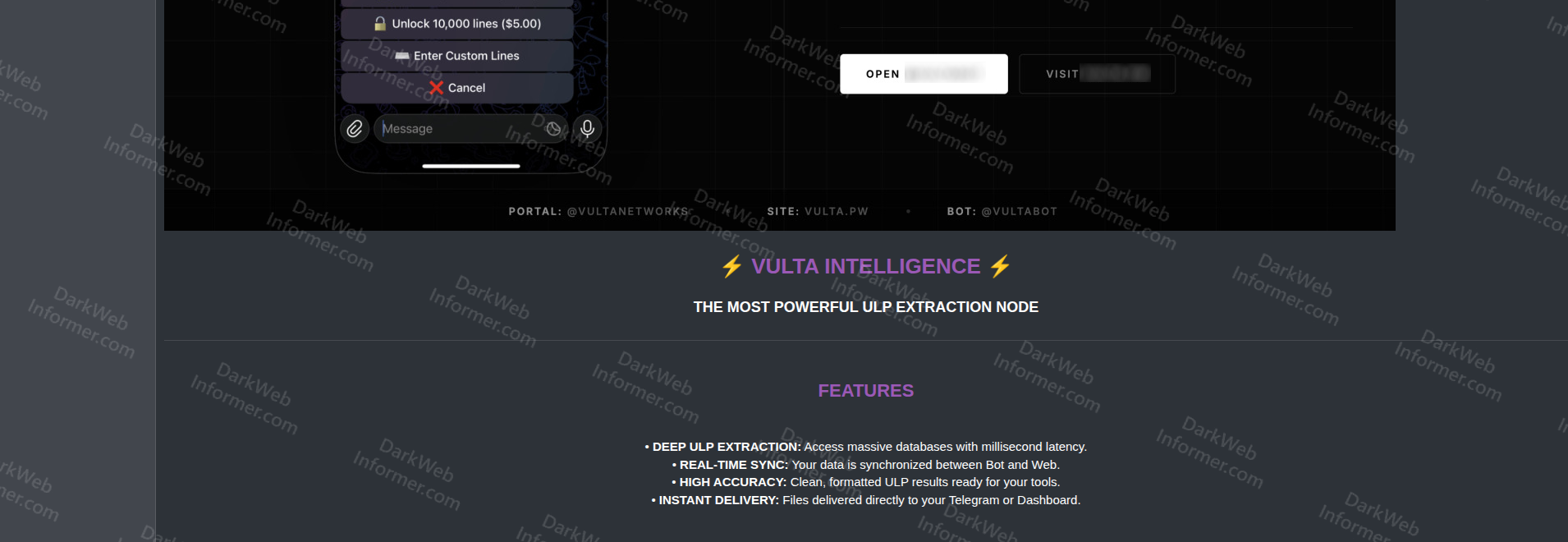
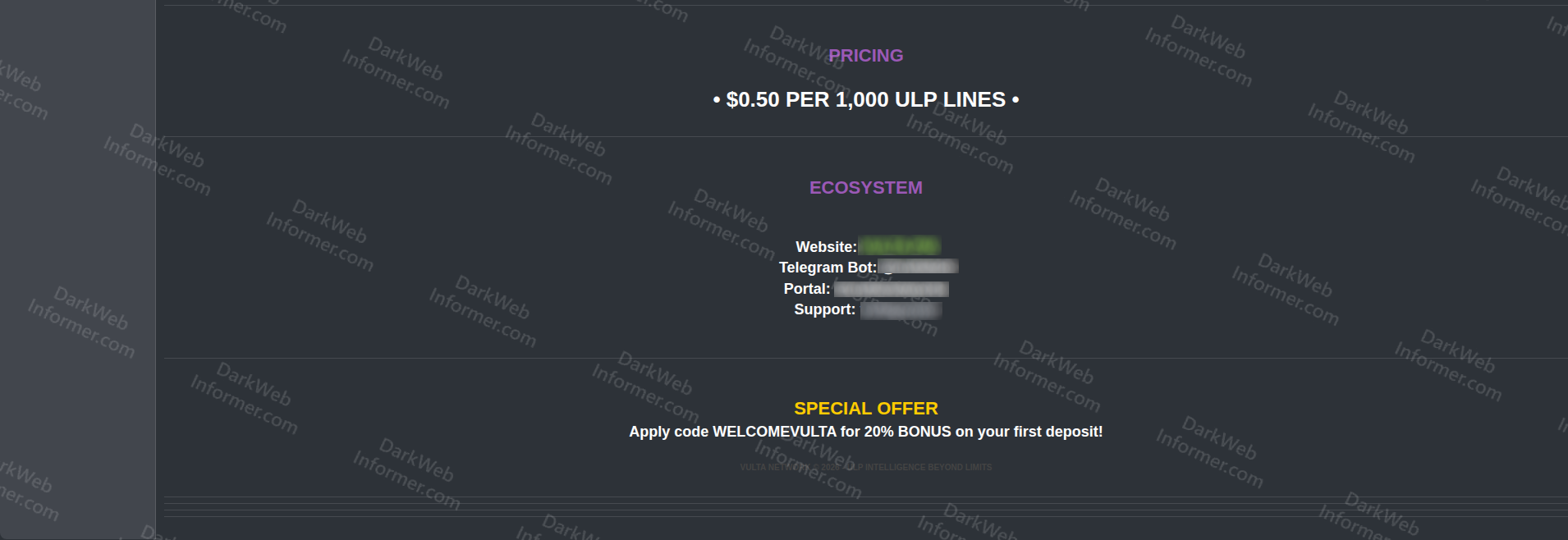
- Extraction: Users select a tier (1,000 lines for $0.50, 5,000 lines for $2.50, 10,000 lines for $5.00) or enter a custom line count.
- Delivery: Clean URL:Login:Password files are delivered instantly to the user's Telegram chat or web dashboard.
The service advertises several key features:
- Deep ULP Extraction: Access to massive databases with millisecond latency.
- Real-Time Sync: Data is synchronized between the Telegram bot and web interface.
- High Accuracy: Clean, formatted ULP results described as ready for use with existing tools.
- Instant Delivery: Files delivered directly to Telegram or the dashboard.
The ecosystem includes a Telegram bot (@VULTABOT), a web portal (@VULTANETWORKS), the main site (vulta.pw), and a support channel. A promotional code (WELCOMEVULTA) offers a 20% bonus on the first deposit. Credits are deposited via cryptocurrency. The 14.2 billion record claim and the Binance search returning 4.1 million hits suggest the database is aggregated from multiple large-scale infostealer log collections.