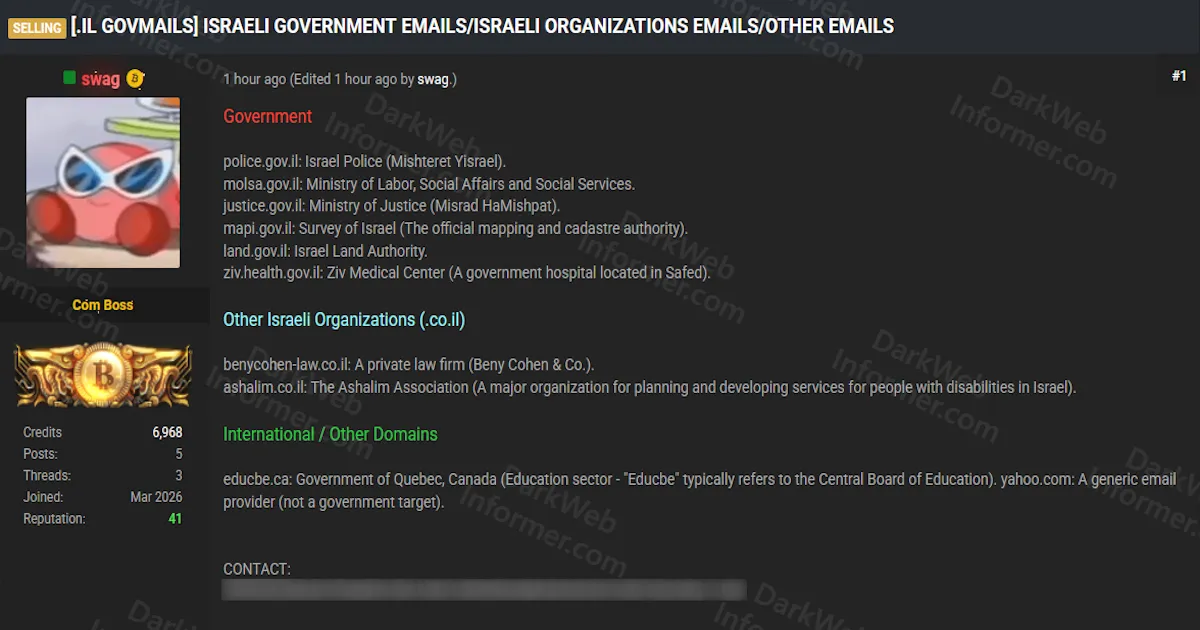
Threat Actor Selling Email Credentials for Israeli Government Agencies, Organizations, and International Targets Including Israel Police, Ministry of Justice, and Quebec Education Board
Quick Facts
Incident Overview
A threat actor going by swag is selling compromised email credentials from multiple Israeli government agencies, Israeli organizations, and international targets. The listing organizes the affected entities into three categories, with the bulk of the targets being Israeli .gov.il government domains. This represents a significant credential exposure across some of Israel's most sensitive public institutions.
The affected entities are organized as follows:
- Israeli Government (.gov.il): Israel Police (Mishteret Yisrael), Ministry of Labor, Social Affairs and Social Services (MOLSA), Ministry of Justice (Misrad HaMishpat), Survey of Israel (the official mapping and cadastre authority), Israel Land Authority, and Ziv Medical Center (a government hospital located in Safed).
- Israeli Organizations (.co.il): Beny Cohen and Co. (a private law firm), and the Ashalim Association (a major organization for planning and developing services for people with disabilities in Israel).
- International / Other Domains: The Quebec Central Board of Education in Canada (education sector), and Yahoo email accounts (described as a generic email provider, not a government target).
The inclusion of Israel Police, Ministry of Justice, and Ministry of Labor credentials is particularly concerning from a national security perspective, as compromised government email accounts can be used for spear phishing against other government employees, accessing internal communications, pivoting deeper into government networks, or conducting social engineering against citizens who trust official government correspondence. The Ziv Medical Center credentials add a healthcare dimension, potentially exposing patient communications or internal hospital systems.