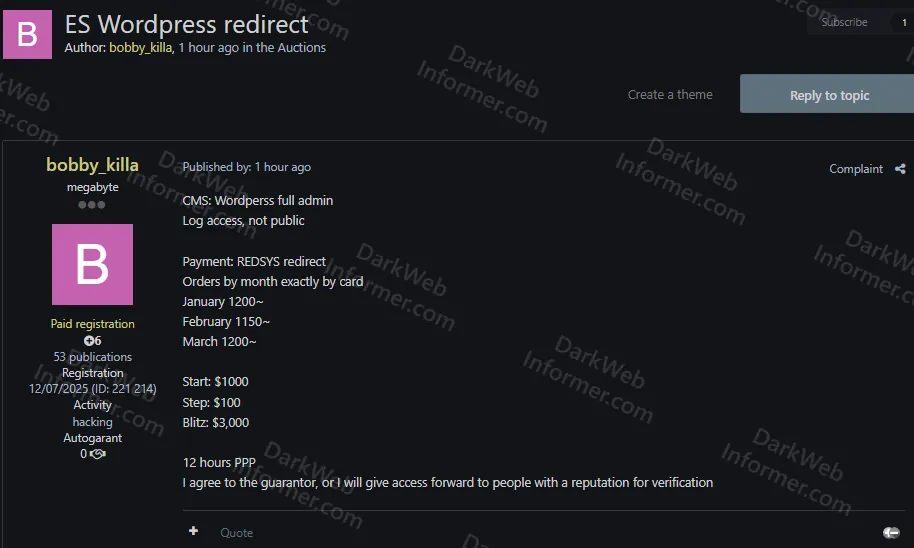
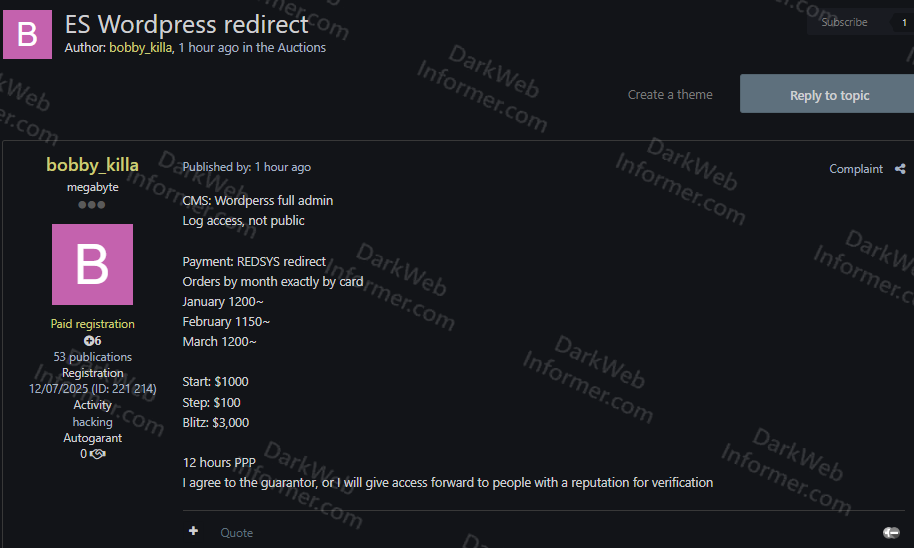
Threat Actor Auctioning WordPress Admin Access to Spanish E-Commerce Site With REDSYS Payment Gateway and ~1,200 Monthly Card Orders
Quick Facts
Incident Overview
A threat actor going by bobby_killa is auctioning full WordPress admin access to an unnamed Spanish e-commerce website that processes payments through REDSYS, Spain's dominant card payment processing system used by the vast majority of Spanish banks and online retailers. The listing is posted in the auctions section of a Russian-language forum and includes specific monthly order volumes, making this a financially motivated access sale rather than a data breach.
The listing details the following:
- Access Level: Full WordPress administrator with complete CMS control over the site.
- Log Access: Available but described as "not public," suggesting the logs are accessible through the admin panel but not exposed externally.
- Payment System: REDSYS redirect, meaning the site processes card payments through Spain's national payment infrastructure. This is the key value of the listing for financially motivated buyers.
- Transaction Volume: January saw approximately 1,200 card orders, February approximately 1,150, and March approximately 1,200, showing consistent monthly payment volume.
The primary risk here is payment fraud. A buyer with WordPress admin access to a site processing ~1,200 monthly REDSYS card transactions could inject payment skimmers, redirect payment flows, modify checkout pages, access stored customer and order data, or use the site's legitimate merchant account for fraudulent transactions. REDSYS processes the majority of card payments in Spain, so a compromised REDSYS-integrated store is a high-value target for carders and financial fraud operators.