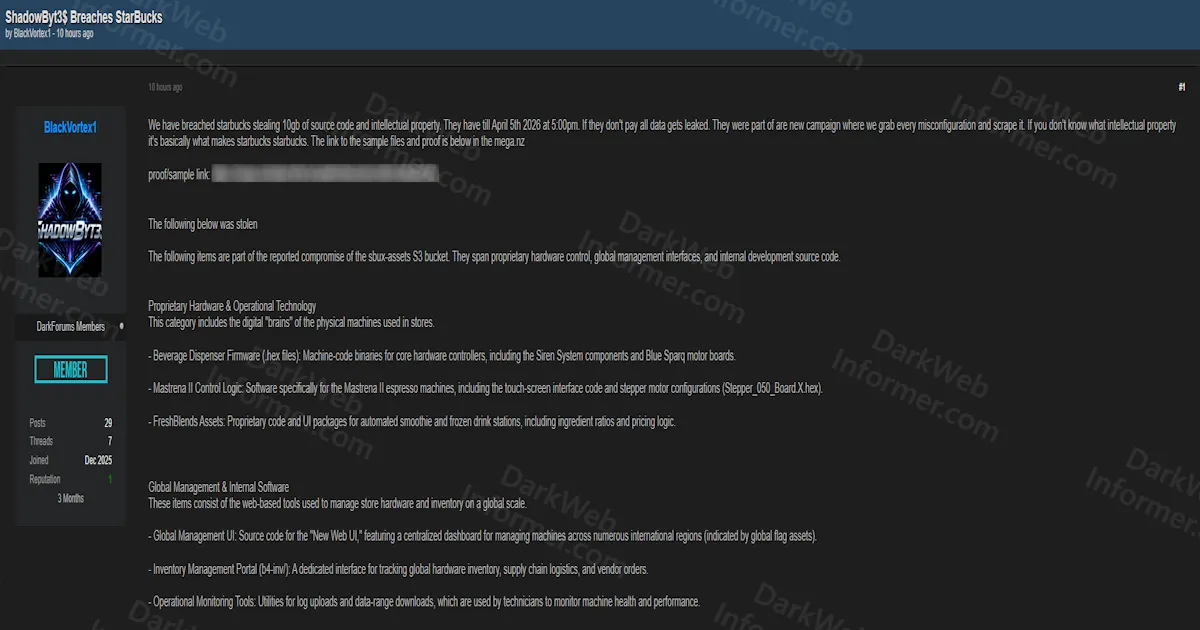
ShadowByt3s Claims Starbucks Breach With 10GB of Proprietary Source Code, Beverage Machine Firmware, and Global Management Tools From Compromised S3 Bucket
Quick Facts
Incident Overview
A threat group calling themselves ShadowByt3s, posted by the actor BlackVortex1, claims to have breached Starbucks by compromising the sbux-assets S3 bucket and exfiltrating 10GB of proprietary intellectual property including source code, firmware, and global management tools. The group describes this as part of a new campaign targeting misconfigured cloud assets and has set a ransom deadline of April 5, 2026 at 5:00 PM, after which they state all data will be publicly leaked.
The stolen data is organized into four categories, all originating from the sbux-assets S3 bucket:
- Proprietary Hardware and Operational Technology: Beverage dispenser firmware in hex file format for core hardware controllers, including Siren System components and Blue Sparq motor boards. Mastrena II espresso machine control logic including touch-screen interface code and stepper motor configurations (Stepper_050_Board_X.hex). FreshBlends proprietary code and UI packages for automated smoothie and frozen drink stations, including ingredient ratios and pricing logic.
- Global Management and Internal Software: Source code for the Global Management UI ("New Web UI") featuring a centralized dashboard for managing machines across international regions with global flag assets. Inventory Management Portal (b4-inv/) for tracking global hardware inventory, supply chain logistics, and vendor orders. Operational monitoring tools for log uploads and data-range downloads used by technicians to monitor machine health and performance.
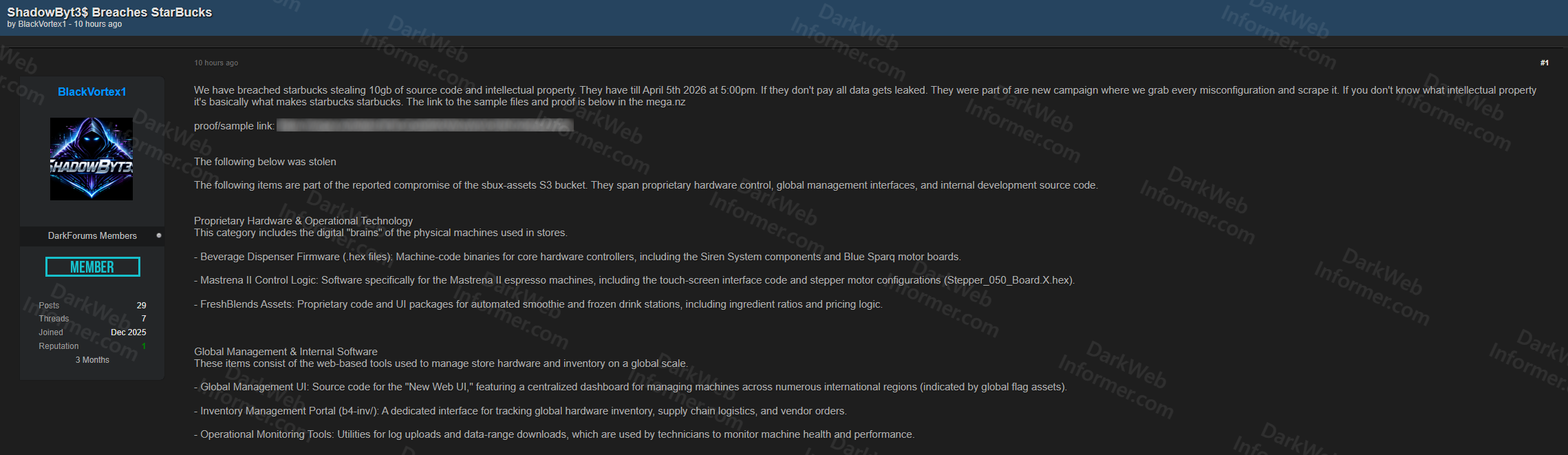
- Developer Environment and Source Code: JavaScript bundles containing hardcoded API endpoints, internal service URLs, and authentication logic. SCSS source files for management interface styling. Source maps (.map files) that allow minified production code to be reconstructed into human-readable format. Developer backup and staging folders (v-2a-upload-problem, b4-temp-download) that may contain temporary credentials or internal developer notes.
- Visual and Brand Assets: Internal staff avatars and profile pictures for system administrators and developers. High-resolution Starbucks corporate branding and partner vendor logos (Blue Sparq) used in internal-only applications.
The group provided proof and sample links via Mega.nz, with a Telegram channel for files exceeding 1GB. They are also actively recruiting corporate insiders with a 30/70 revenue split (30% to the insider, 70% to the group) with no upfront cost required. The actor's forum account was created in December 2025 with 29 posts, 7 threads, and a reputation of 1.
The firmware and OT exposure is the most critical element of this breach. Hex files for beverage dispensers, espresso machine stepper motor configurations, and automated smoothie station code represent the proprietary control logic for physical machines deployed in tens of thousands of Starbucks locations globally. In the wrong hands, this could enable hardware manipulation, supply chain attacks against Starbucks equipment, or competitive reverse engineering of their beverage automation technology.