Noobsaibot HVNC Advertised as Next-Generation Stealer and RAT With Zero-Disk Footprint, Chrome V20 Bypass, Monolithic Architecture, and Guaranteed Zero AV Detections
Quick Facts
Incident Overview
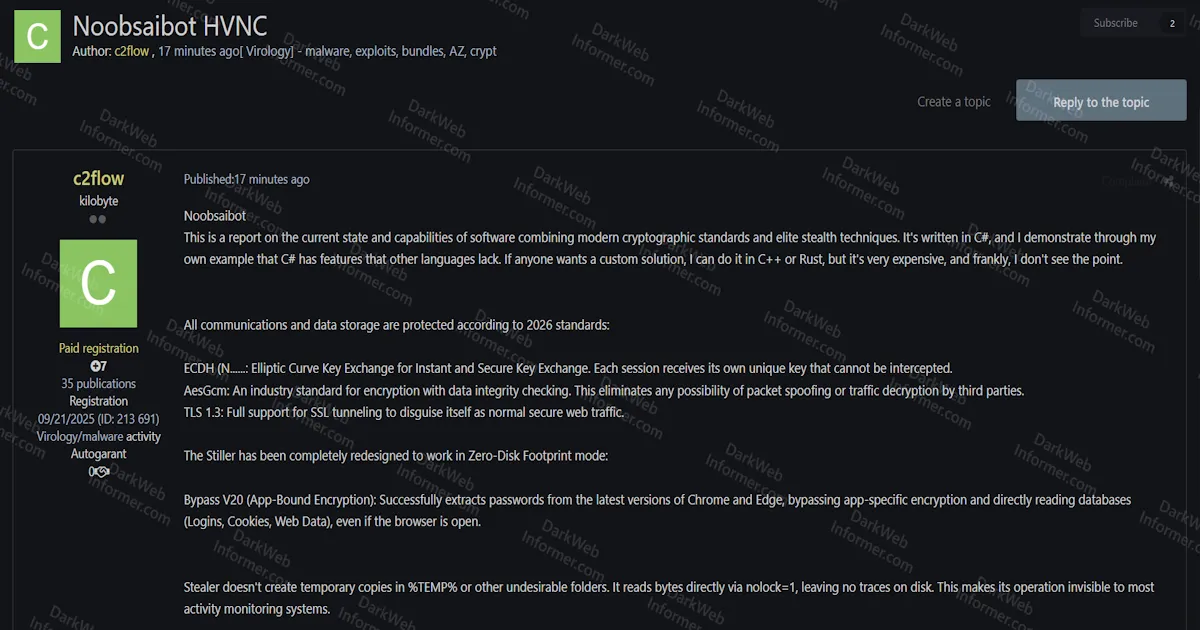
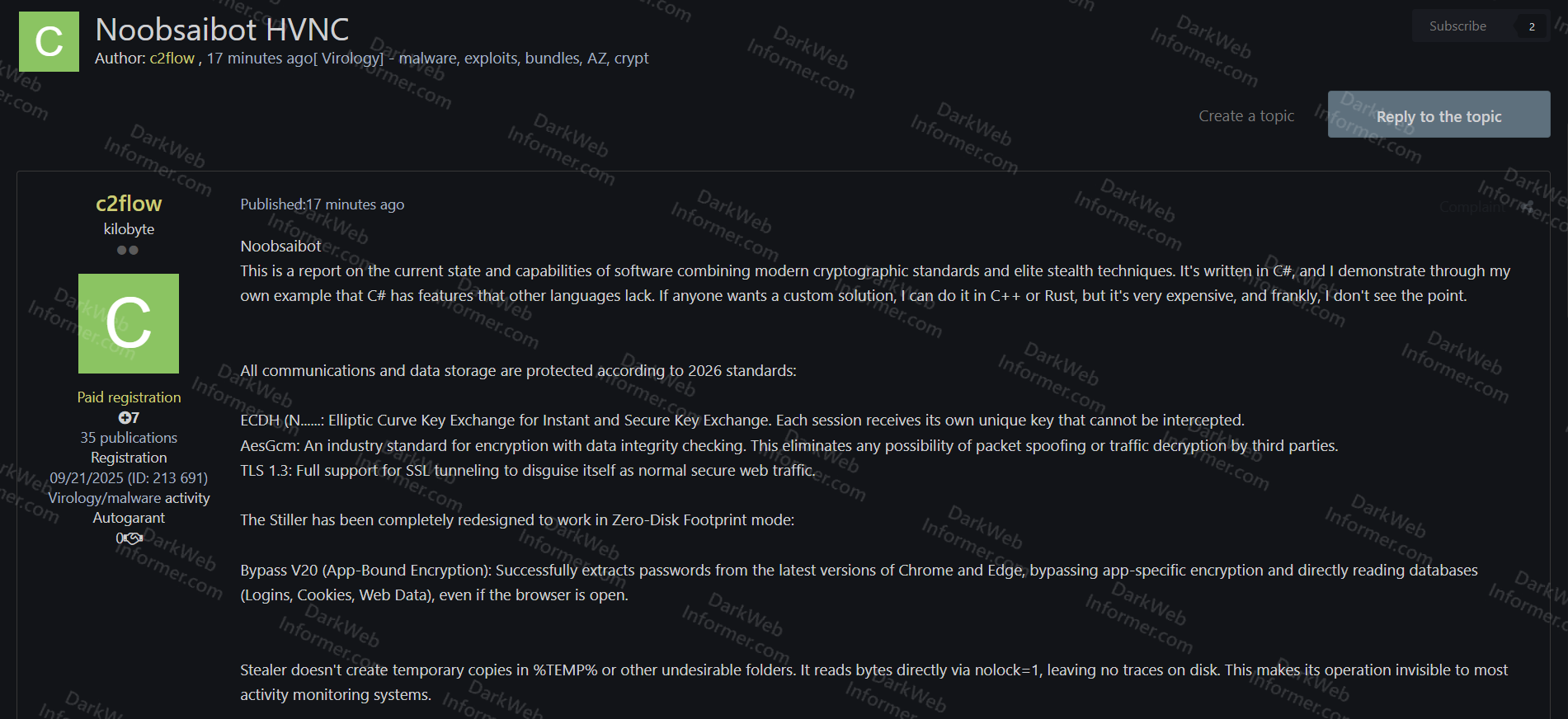
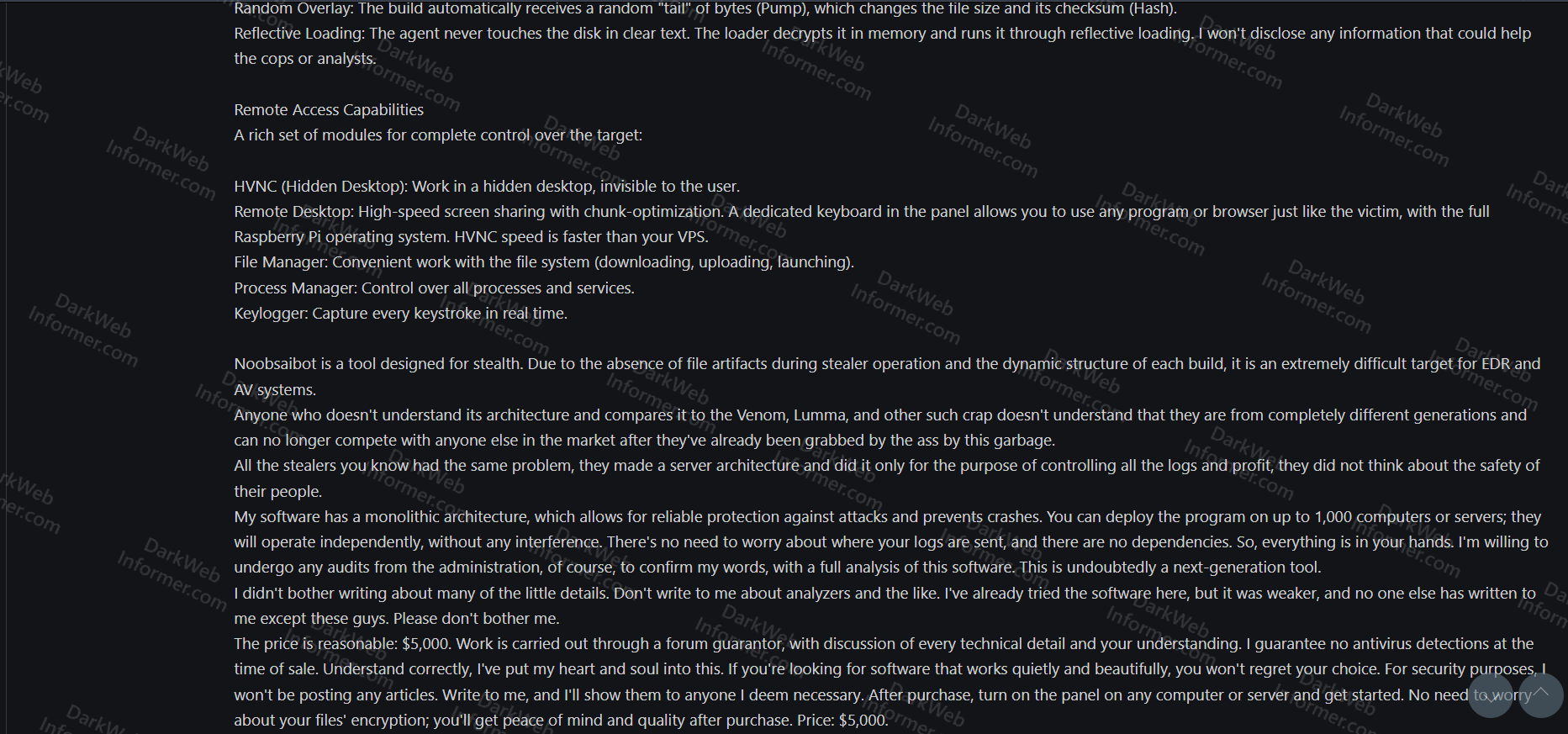
A threat actor going by c2flow is advertising Noobsaibot, a C# combined stealer, HVNC, and remote access tool that the developer positions as architecturally distinct from existing stealers like Venom, Lumma, and similar tools. The actor claims the tool represents a generational leap in stealer design, with a monolithic architecture that eliminates external server dependencies and allows each deployment to operate independently. The listing is priced at $5,000 with a guarantee of zero antivirus detections at time of sale, transacted through a forum guarantor.
The tool's capabilities break down into several categories:
- Communications Security: ECDH elliptic curve key exchange for per-session unique keys, AES-GCM encryption with data integrity checking to prevent packet spoofing or traffic decryption, and TLS 1.3 support for SSL tunneling that disguises traffic as normal secure web browsing.
- Zero-Disk Footprint Stealer: Bypasses Chrome and Edge App-Bound Encryption (V20) to extract passwords, logins, cookies, and web data directly from browser databases even while the browser is open. Creates no temporary copies in %TEMP% or other folders, reading bytes directly via nolock=1 to leave no disk traces.
- Evasion: Random overlay ("pump") that appends random bytes to each build, changing file size and hash every time. Reflective loading where the agent never touches disk in clear text, decrypting in memory only. Dynamic build structure makes each instance unique to EDR and AV systems.
- Remote Access: HVNC (Hidden Virtual Network Computing) for invisible desktop access, standard remote desktop with chunk-optimized screen sharing and full Raspberry Pi keyboard emulation, file manager for downloading/uploading/launching files, process manager for controlling all processes and services, and a keylogger capturing every keystroke in real time.
- Architecture: Monolithic design with no external dependencies or server infrastructure. Scales to 1,000 computers or servers operating independently. The operator controls where logs are sent and maintains full ownership of the panel and deployments.
The actor is vocal about differentiating Noobsaibot from existing stealers, claiming that competitors built server-based architectures focused on controlling logs and profits rather than operator safety, and that those tools are now outdated. The developer claims to be willing to undergo forum administration audits to verify the tool's capabilities. Custom builds in C++ or Rust are mentioned as available but described as very expensive.