FulcrumSec Breaches Unique Computing, ReFocus AI, and Gennet AI Exposing 23,000 Insurance Policyholders, $797M in Premiums, Driver Licenses, SSNs, and Proprietary ML Models From a Single Unpatched AWS Account
Quick Facts
Incident Overview
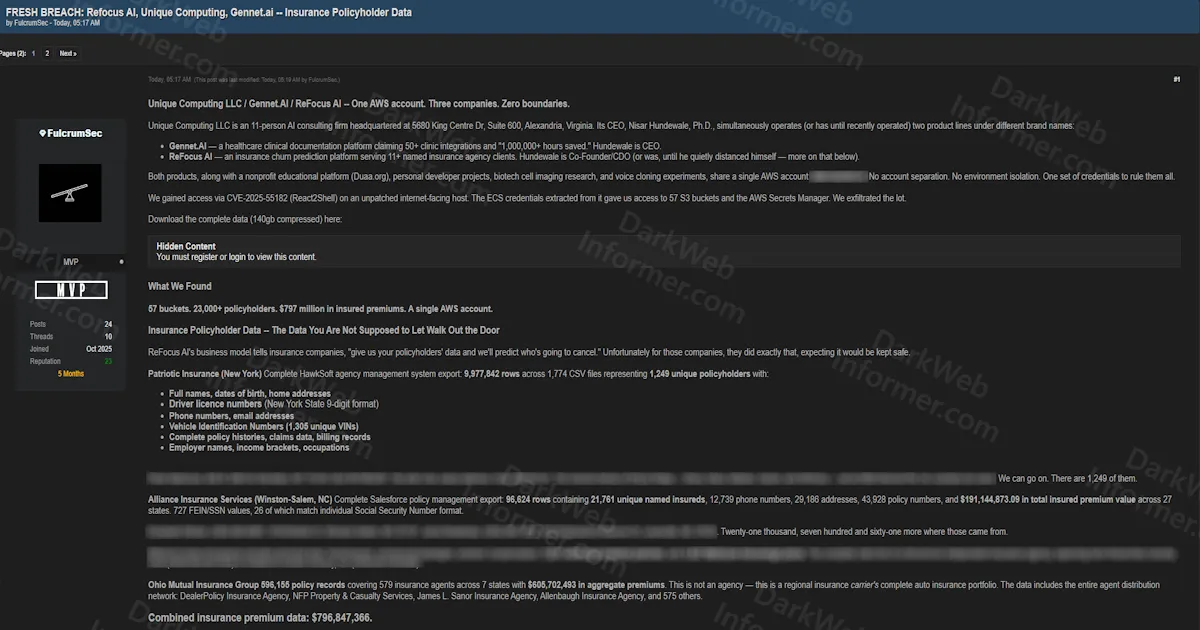
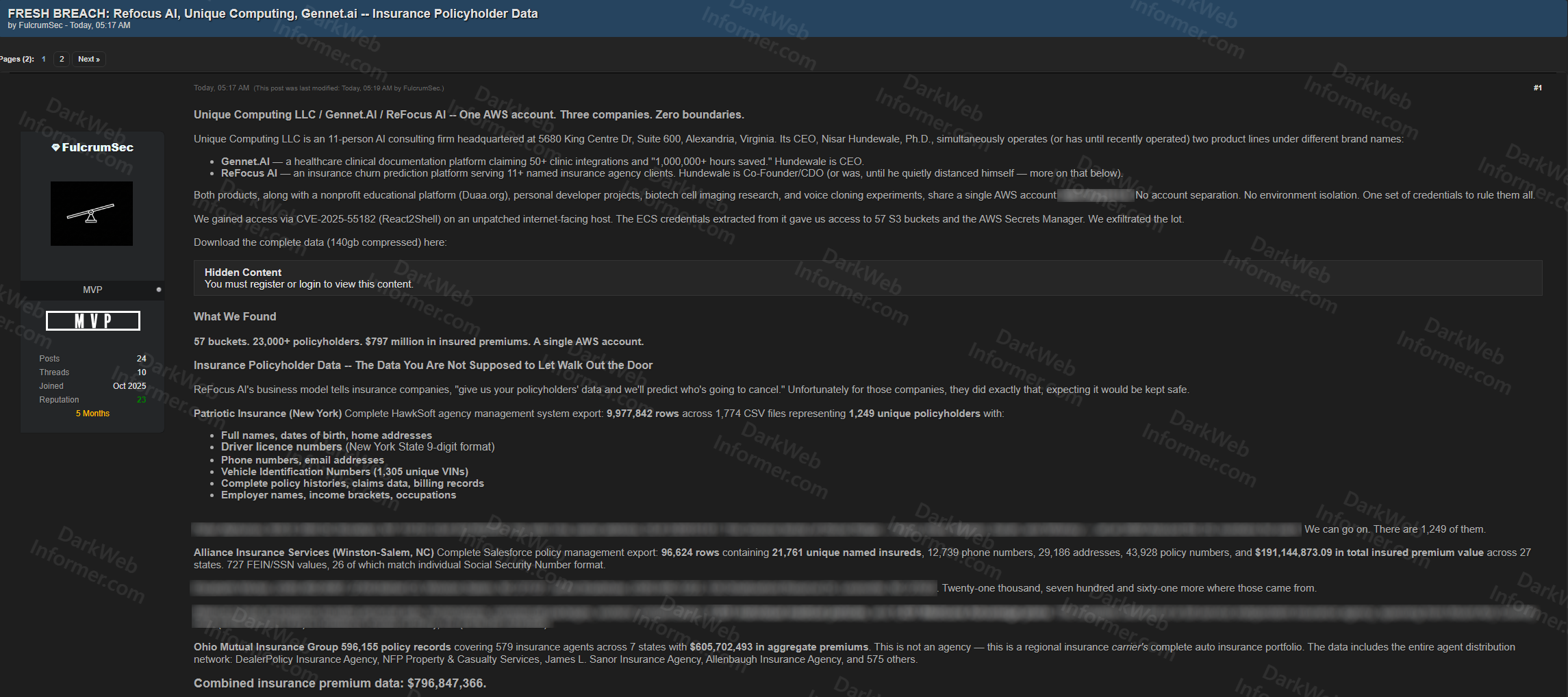
FulcrumSec has published a detailed breach report and 140GB data dump targeting three interconnected companies operating under a single AWS account: Unique Computing LLC (an 11-person AI consulting firm in Alexandria, Virginia), Gennet AI (a healthcare clinical documentation platform), and ReFocus AI (an insurance churn prediction platform serving 11+ insurance agency clients). The breach was achieved through CVE-2025-55182 (React2Shell) on an unpatched internet-facing host, which yielded ECS credentials providing access to 57 S3 buckets and the AWS Secrets Manager.
The core finding is that all three companies, along with a nonprofit educational platform (Duaa.org) and personal developer projects, shared a single AWS account (086134439114) with no account separation, no environment isolation, and one set of credentials controlling everything. The actor describes this as having one compromised key that grants access to everything from a children's math curriculum to insurance policyholder driver license numbers.
The insurance policyholder data is the most damaging component, totaling $796,847,366 in aggregate insured premiums across 11+ agencies:
- Patriotic Insurance (New York): Complete HawkSoft agency management export across 1,774 CSV files with 9,977,842 rows representing 1,249 unique policyholders. Includes full names, dates of birth, home addresses, driver license numbers (NY State 9-digit format), phone numbers, email addresses, 1,305 unique VINs, complete policy histories, claims data, billing records, employer names, income brackets, and occupations.
- Alliance Insurance Services (Winston-Salem, NC): Complete Salesforce policy management export with 96,624 rows containing 21,761 unique named insureds, 12,739 phone numbers, 29,186 addresses, 43,928 policy numbers, and $191,144,873 in total insured premium value across 27 states. Includes 727 FEIN/SSN values, 26 matching individual Social Security Number format, 7,231 individual medical policies, and 1,431 Medicare Advantage plans.
- Ohio Mutual Insurance Group: 596,155 policy records covering 579 insurance agents across 7 states with $605,702,493 in aggregate premiums. This is a regional insurance carrier's complete auto insurance portfolio including the entire agent distribution network.
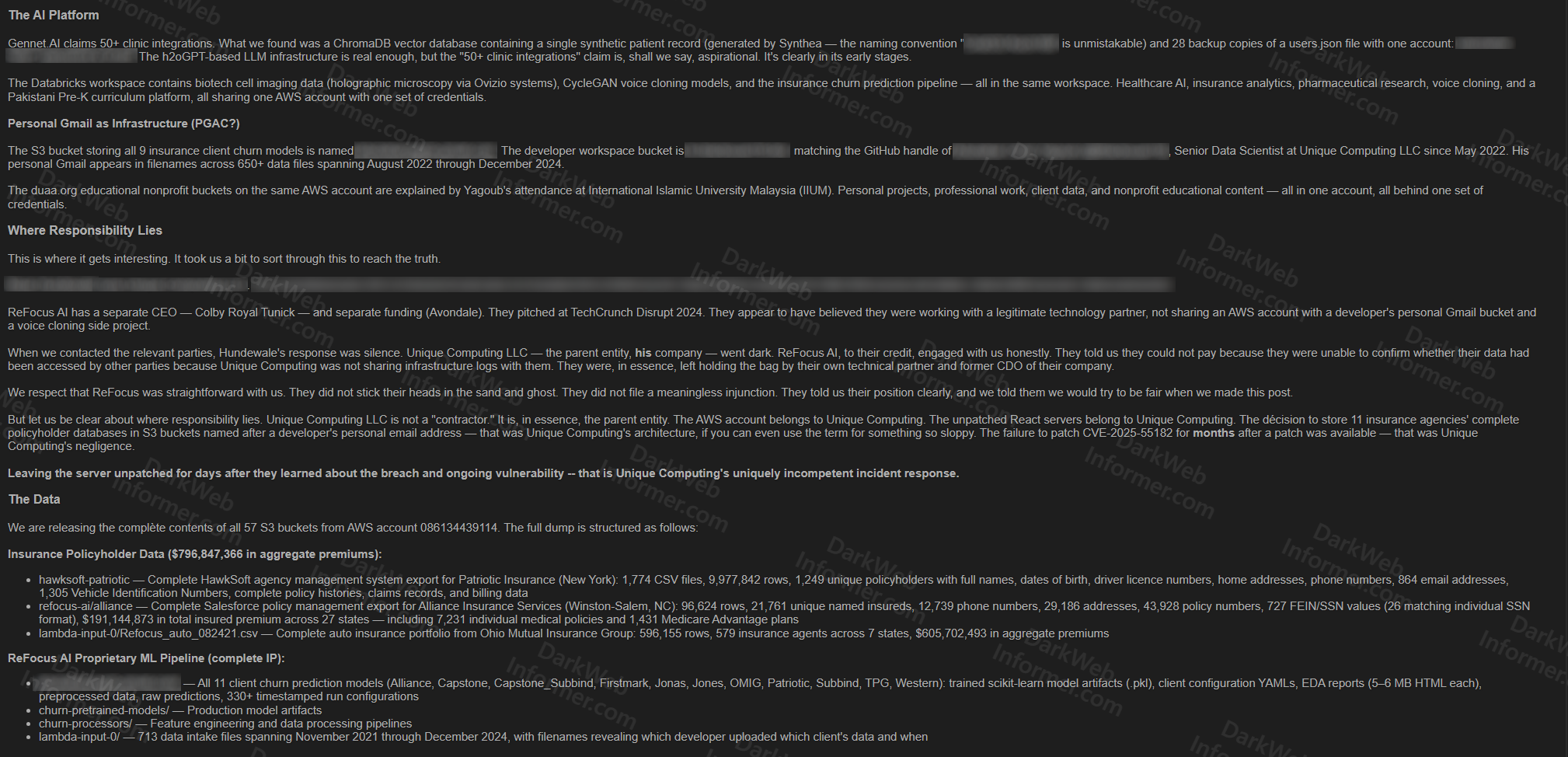
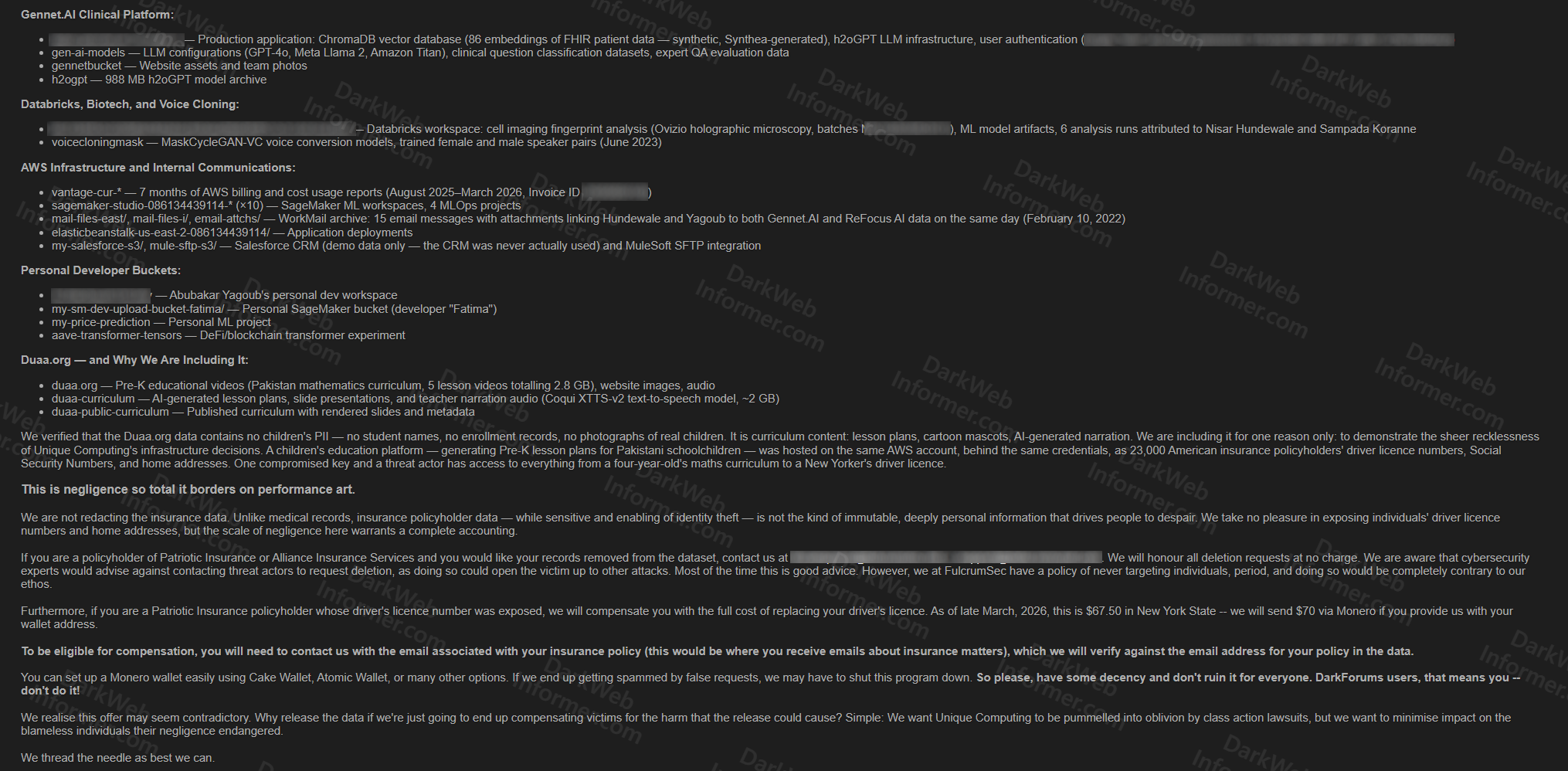
Beyond the insurance data, the breach exposed ReFocus AI's proprietary ML pipeline including all 11 client churn prediction models (trained scikit-learn artifacts, client configuration YAMLs, EDA reports, preprocessed data, raw predictions, and 330+ timestamped run configurations), production model artifacts, feature engineering pipelines, and 713 data intake files spanning November 2021 through December 2024. The Gennet AI clinical platform contained a ChromaDB vector database with synthetic FHIR patient data, h2oGPT LLM infrastructure, and LLM configurations for GPT-4o, Meta Llama 2, and Amazon Titan.
Additional S3 buckets contained Databricks workspaces with biotech cell imaging analysis (Ovizio holographic microscopy), CycleGAN voice cloning models, 7 months of AWS billing and cost usage reports, 10 SageMaker ML workspaces, WorkMail archives linking the companies' principals, Elastic Beanstalk application deployments, personal developer buckets, and the Duaa.org children's education platform (Pre-K Pakistani mathematics curriculum). The actor verified the education content contains no children's PII.
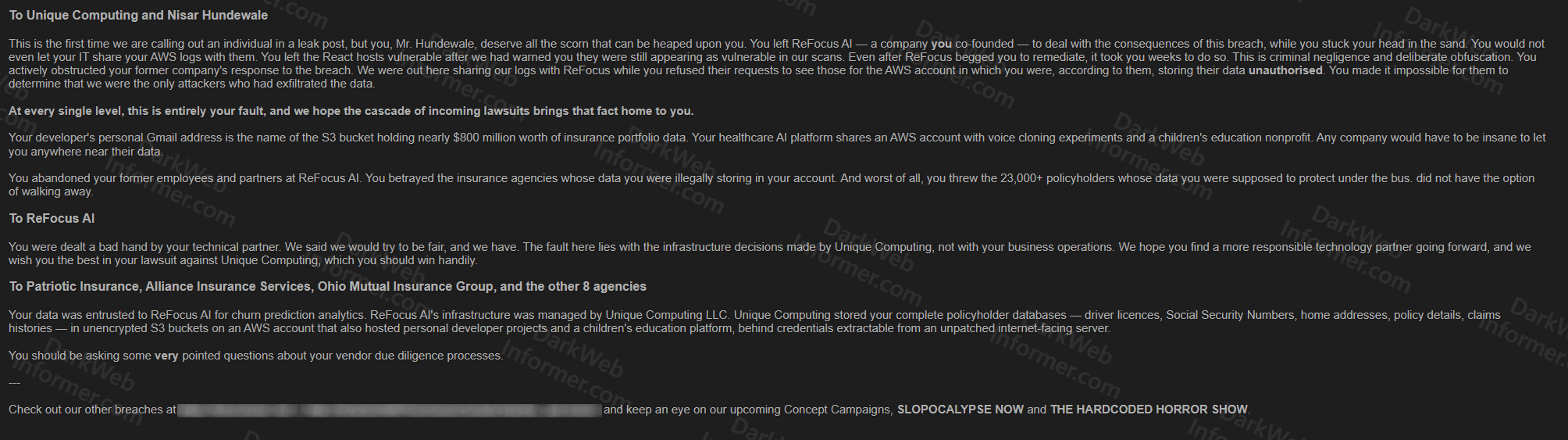
FulcrumSec's post directly addresses Unique Computing's CEO, naming them personally and accusing the company of criminal negligence for failing to patch CVE-2025-55182 for months after a patch was available, refusing to share infrastructure logs with ReFocus AI after the breach was discovered, and leaving the React hosts vulnerable even after being warned. The actor states ReFocus AI cooperated when contacted, acknowledged they could not pay because they were unable to confirm whether their data had been accessed by other parties, and that Unique Computing "went dark." FulcrumSec is offering to compensate affected Patriotic Insurance policyholders $70 in Monero for driver's license replacement costs, verified against the leaked data.