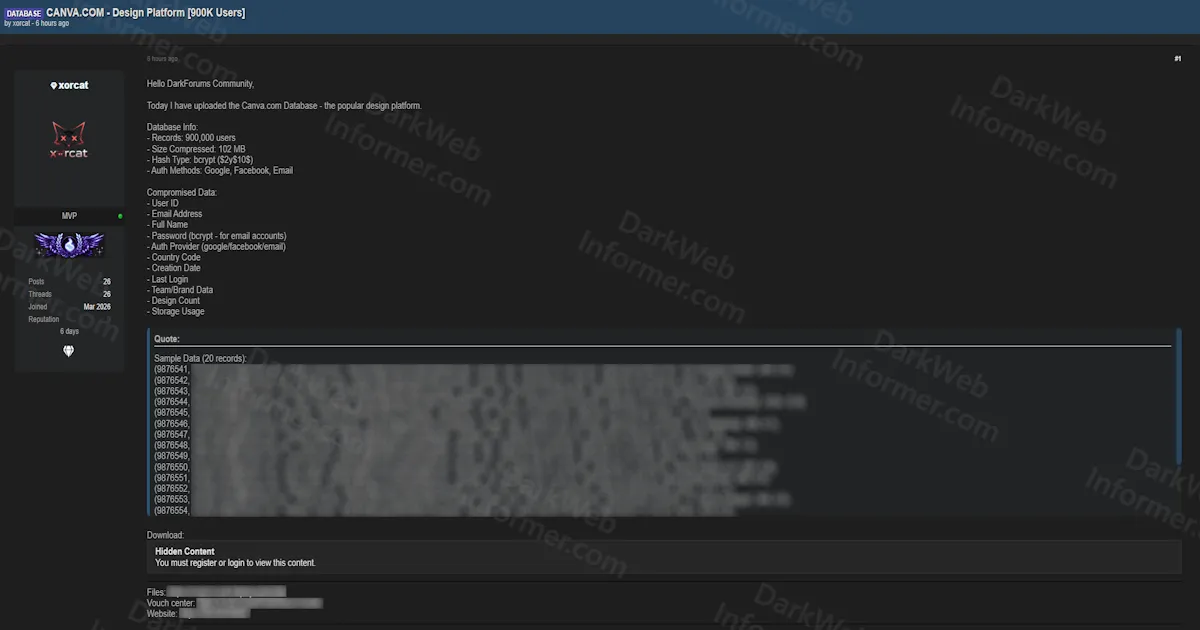
Alleged Database Leak of Canva Exposes 900,000 User Records With Bcrypt Passwords, OAuth Providers, and Design Platform Usage Data
Quick Facts
Incident Overview
A threat actor going by xorcat has uploaded a database allegedly from Canva, the widely used Australian design platform with over 170 million monthly active users worldwide. The leaked dataset contains 900,000 user records and has been published as a free download for registered forum members. The actor provided a 20-record sample to demonstrate the data's structure and authenticity.
The dataset contains the following fields per user record:
- Account Identifiers: User IDs, email addresses, and full names.
- Credentials: Passwords hashed with bcrypt ($2y$10$), which is a strong hashing algorithm. Unlike MD5 or SHA1 leaks, bcrypt hashes are computationally expensive to crack, though weak passwords are still vulnerable to targeted attacks.
- Authentication Providers: Which OAuth method each user signed up with (Google, Facebook, or email), revealing which third-party accounts are linked to each Canva profile.
- Geographic Data: Country codes for each user.
- Account Metadata: Creation dates and last login timestamps, showing when accounts were created and when they were most recently active.
- Platform Usage: Team/brand data, design counts, and storage usage, which reveals how actively each user engages with the platform and whether they are individual or enterprise users.
It's worth noting that Canva previously experienced a major breach in May 2019 that affected 137 million users. This appears to be a separate, smaller dataset of 900,000 records. The inclusion of design counts, storage usage, and team/brand data is particularly useful for identifying high-value enterprise accounts, professional designers, and business users who may store sensitive client work on the platform.