Alleged Breach of Smarteez Exposes Full Production Database for L'Oreal Morocco Including 296 Pharmacies, 361K Sales Records, OAuth Secrets, and Competitive Intelligence Across Four L'Oreal Brands
Quick Facts
Incident Overview
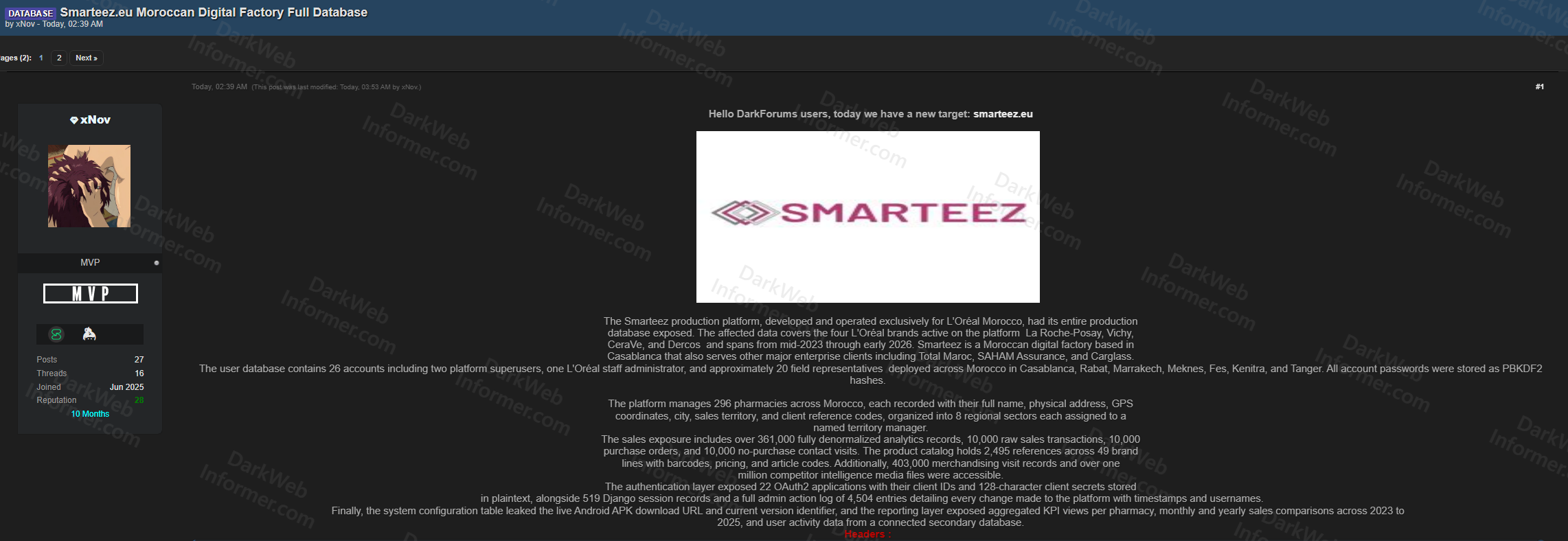
A threat actor going by xNov has leaked the complete production database of Smarteez, a Moroccan digital factory based in Casablanca that was developed and operated exclusively for L'Oreal Morocco. Smarteez also serves other major enterprise clients including Total Maroc, SAHAM Assurance, and Carglass. The exposed data covers four L'Oreal brands active on the platform: La Roche-Posay, Vichy, CeraVe, and Dercos, spanning from mid-2023 through early 2026.
The breach is comprehensive and covers the platform's entire operational footprint across multiple data categories:
- User Accounts: 26 accounts including two platform superusers, one L'Oreal staff administrator, and approximately 20 field representatives deployed across Morocco in Casablanca, Rabat, Marrakech, Meknes, Fes, Kenitra, and Tanger. All passwords stored as PBKDF2 hashes.
- Pharmacy Network: 296 pharmacies across Morocco, each recorded with full name, physical address, GPS coordinates, city, sales territory, and client reference codes, organized into 8 regional sectors with named territory managers.
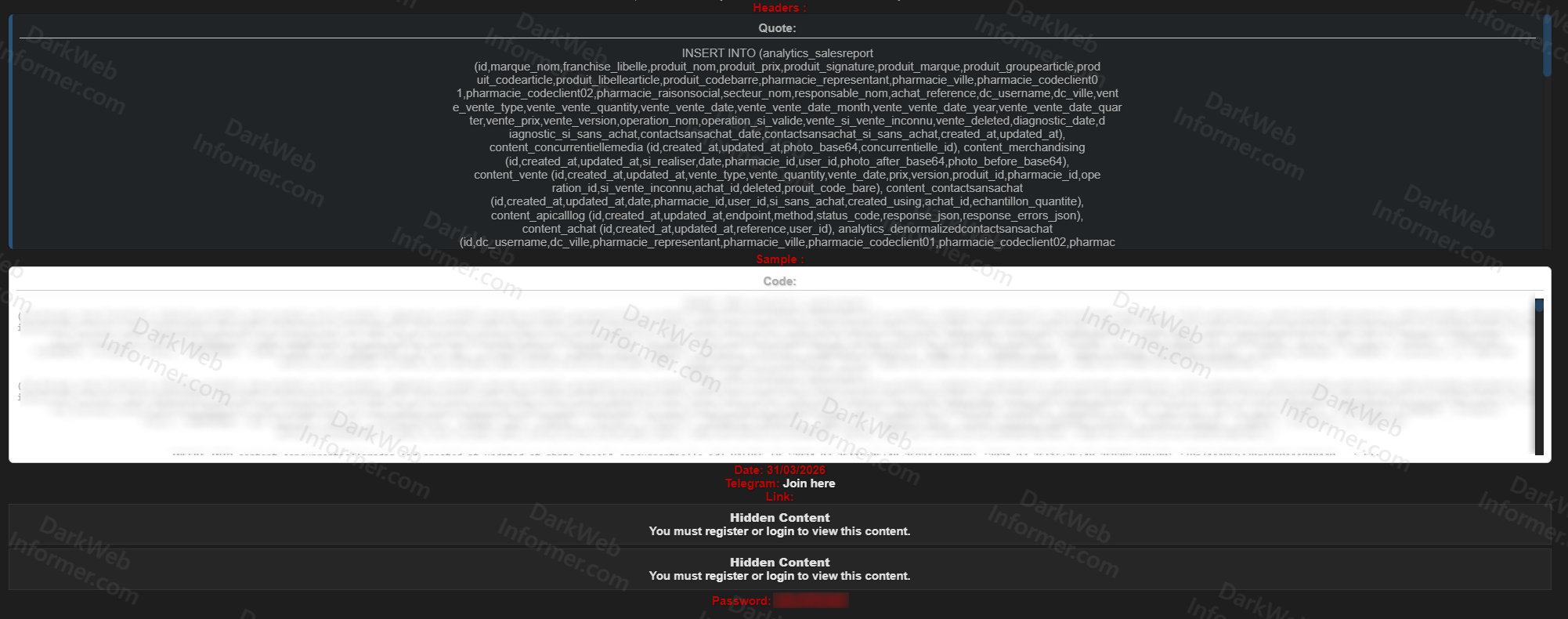
- Sales Data: Over 361,000 fully denormalized analytics records, 10,000 raw sales transactions, 10,000 purchase orders, and 10,000 no-purchase contact visits. The sample SQL data shows individual transaction-level detail including product names, barcodes, pricing, brand, pharmacy name, representative name, and timestamps.
- Product Catalog: 2,495 references across 49 brand lines with barcodes, pricing, and article codes.
- Competitive Intelligence: Over 1 million merchandising visit records and over 1 million competitive intelligence media files, representing L'Oreal Morocco's field intelligence on competitor shelf positioning and retail presence.
- Authentication Layer: 22 OAuth2 applications with their client IDs and 128-character client secrets stored in plaintext, alongside 519 Django session records.
- Admin Audit Trail: Full admin action log of 4,504 entries detailing every change made to the platform with timestamps and usernames.
- System Configuration: The configuration table leaked the live Android APK download URL and current version identifier.
- Reporting Layer: Aggregated KPI views per pharmacy, monthly and yearly sales comparisons across 2023 to 2025, and user activity data from a connected secondary database.
This breach exposes L'Oreal Morocco's complete sales operation infrastructure, field intelligence apparatus, pharmacy distribution network, and product pricing strategy across the country.