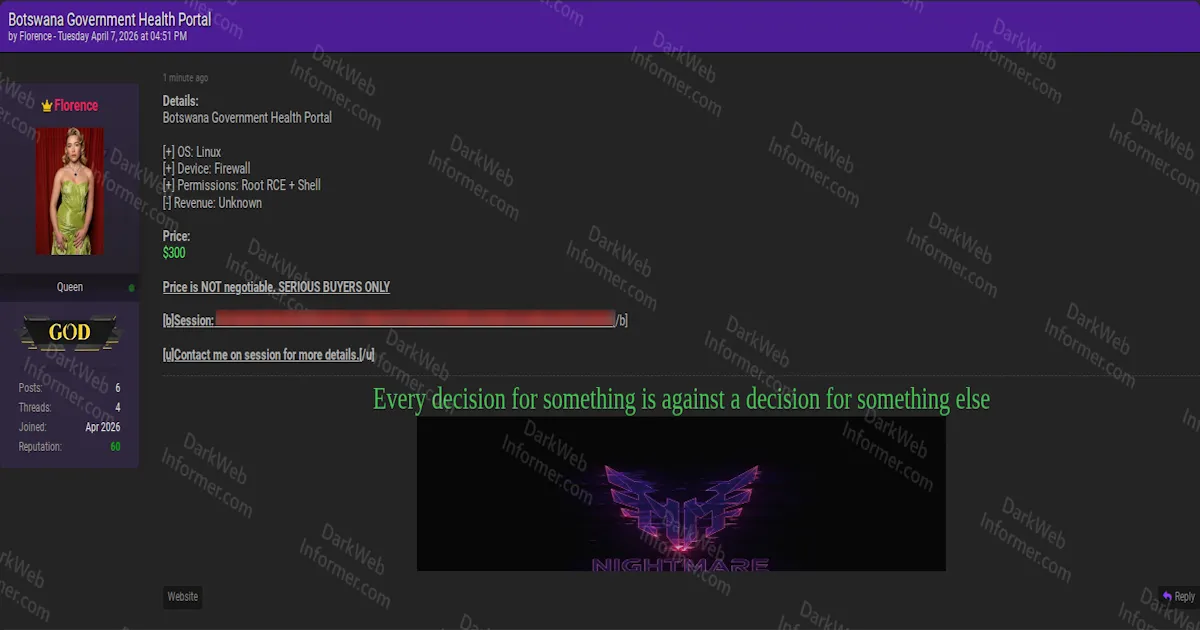
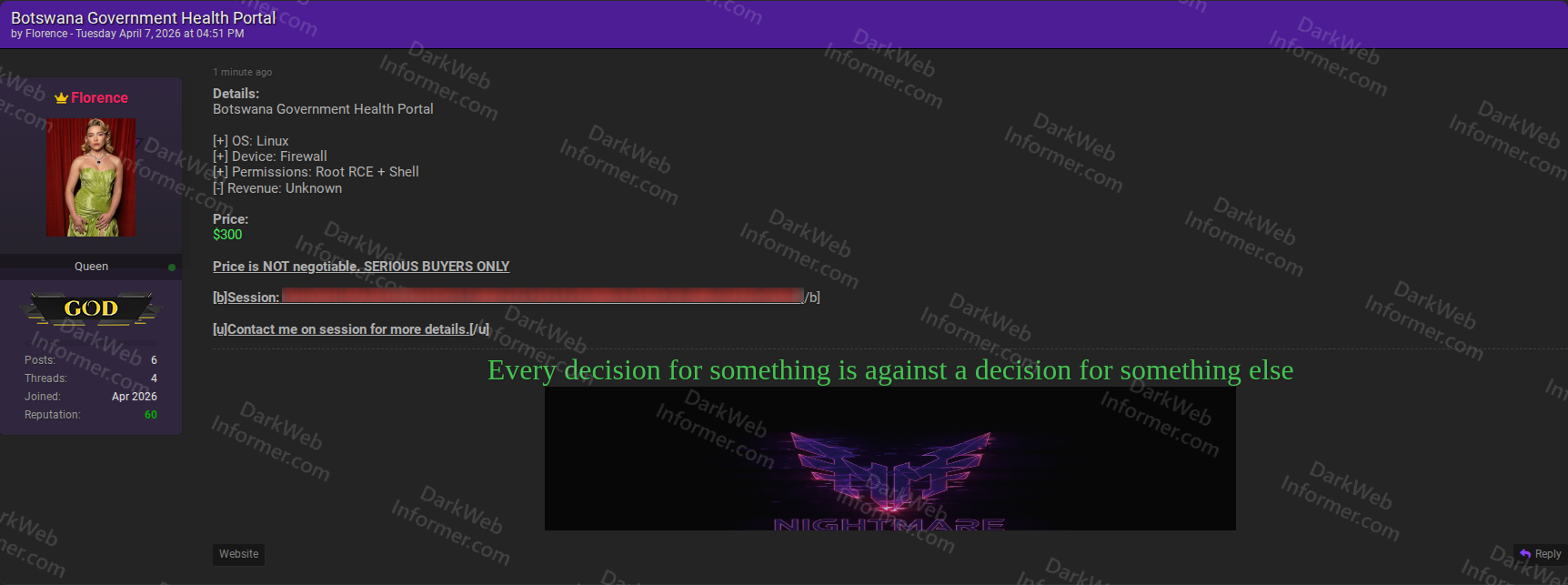
Threat Actor Selling Root RCE Shell Access to Botswana Government Health Portal Firewall for $300
Quick Facts
Incident Overview
A threat actor going by Florence, associated with the Nightmare group, is selling root-level remote code execution and shell access to a firewall device on the Botswana Government Health Portal. The listing is brief but the access being offered is the most dangerous type available: root RCE on a network security appliance protecting government healthcare infrastructure.
The listing specifies the following technical details:
- Operating System: Linux, indicating a Linux-based firewall appliance (common in government deployments, potentially a Fortinet, Palo Alto, Sophos, or similar device running a Linux-based OS).
- Device Type: Firewall, meaning the compromised device sits at the network perimeter and controls traffic flow into and out of the health portal's infrastructure.
- Access Level: Root RCE + Shell, providing the highest possible privilege level on the device with the ability to execute arbitrary commands, modify firewall rules, intercept traffic, and pivot deeper into the network.
- Revenue: Listed as unknown, which is typical for government targets where revenue isn't publicly reported.
Root access to a firewall on a government health portal is particularly dangerous because it provides a position to intercept all network traffic flowing through the device, disable security controls to allow further intrusion, pivot into internal health systems that may contain patient records and sensitive health data, deploy persistent backdoors at the network perimeter level, and modify access rules to allow additional attackers in. The price is fixed at $300 and described as non-negotiable, with contact exclusively through Session messaging.