Polish Eco-Friendly Retailer VegeHome Suffers Data Breach Exposing 100K+ Customers
Quick Facts
Incident Overview
A threat actor going by lulzintel has uploaded the full database of vegehome.pl, a Polish eco-friendly home products retailer. The actor states the breach occurred in April 2026 and exposed data belonging to over 100,000 customers. VegeHome's tagline "inspiracje mamy w naturze" (nature-inspired) positions it as an eco and natural lifestyle brand. The data was published as a free download for registered forum members.
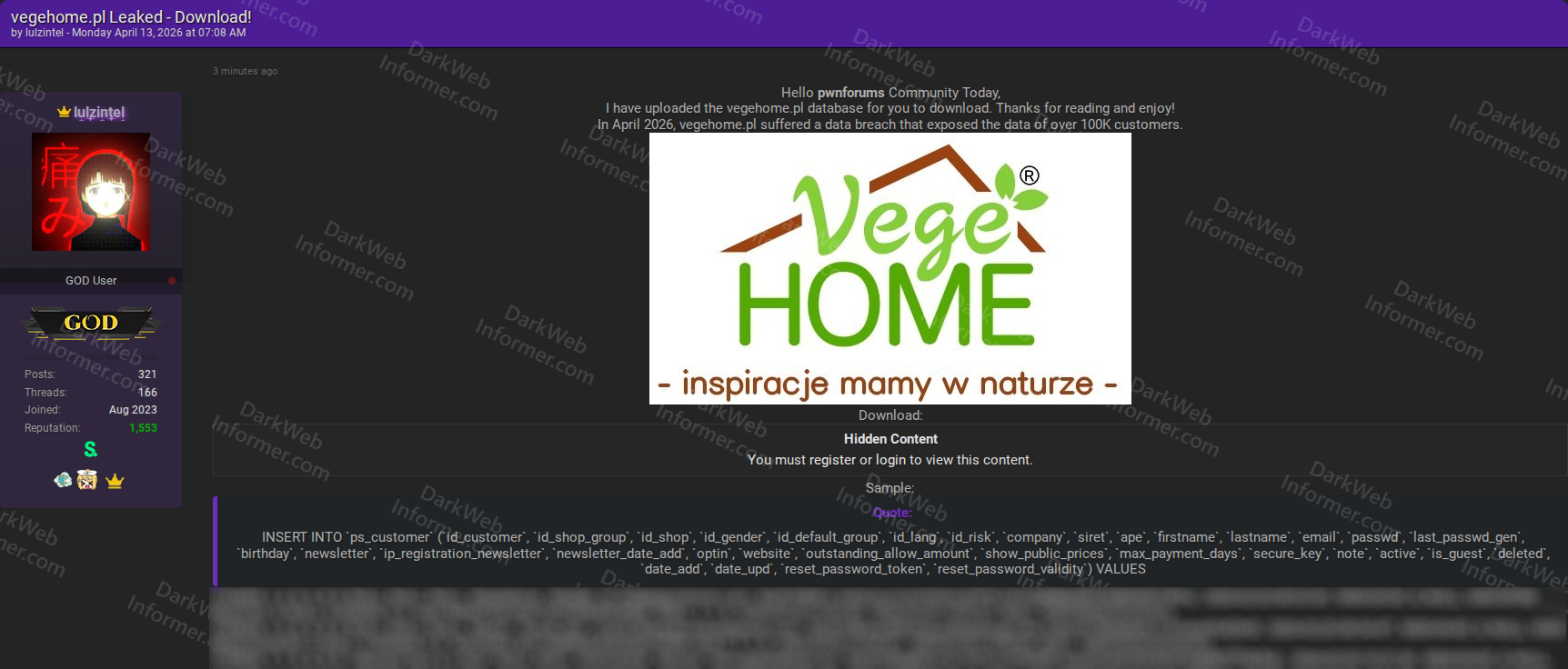
The leaked data comes from a PrestaShop installation (identified by the ps_customer and ps_mail table structures) and contains the following fields:
- Customer Identity: Customer IDs, first names, last names, email addresses, gender IDs, and birthdays.
- Business Details: Company names, SIRET numbers (French/EU business registration identifiers), and APE codes (business activity classification). This suggests VegeHome serves both individual consumers and business customers.
- Credentials and Security: Hashed passwords (passwd field), last password generation timestamps, secure keys, password reset tokens, and password reset validity periods. The reset tokens and secure keys could allow account takeover if they are still valid.
- Account Metadata: Shop group IDs, shop IDs, default group IDs, language IDs, risk IDs, newsletter subscription status, newsletter registration IPs, opt-in status, account creation dates, last update dates, active/deleted/guest flags, and notes.
- Financial Settings: Outstanding allow amounts, show public prices flags, and max payment days, which are typically used for B2B customers with credit terms.
- Mail System: A separate ps_mail table with mail IDs, recipients, templates, subjects, language IDs, and timestamps, exposing the store's internal email communication records with customers.
The combination of password reset tokens, secure keys, and hashed passwords makes this particularly actionable for attackers. If any reset tokens are still valid, they could be used for direct account takeover without needing to crack passwords. The B2B data (SIRET numbers, company names, payment terms) adds a business identity theft dimension beyond typical consumer e-commerce breaches.