Alleged Breach of Colombia's Huila Department Government Extranet Exposes Officer Data, Municipal Offices, and Government Operations Across 8 Municipalities
Quick Facts
Incident Overview
NyxarGroup, in collaboration with three other threat actors (ArcRaidersPlayer, Petro_Escobar, and CryptoDead), claims to be selling data exfiltrated from extranet.huila.gov.co, the government extranet for the Department of Huila in Colombia. This marks NyxarGroup's continued targeting of Latin American government infrastructure, following their earlier breaches of Chile's Ley del Lobby platform and Servicio Civil, and CryptoDead's involvement in the ICFES Colombia data leak.
The breach exposes two main categories of data:
- Officer Information: Government employee records with the following fields: Nombre (name), Cargo (position/title), Tipo (type), Telefono (phone), Correo (email), Entidad (entity/agency), Unidad (unit), Sede (office location), and Grupo (group/department).
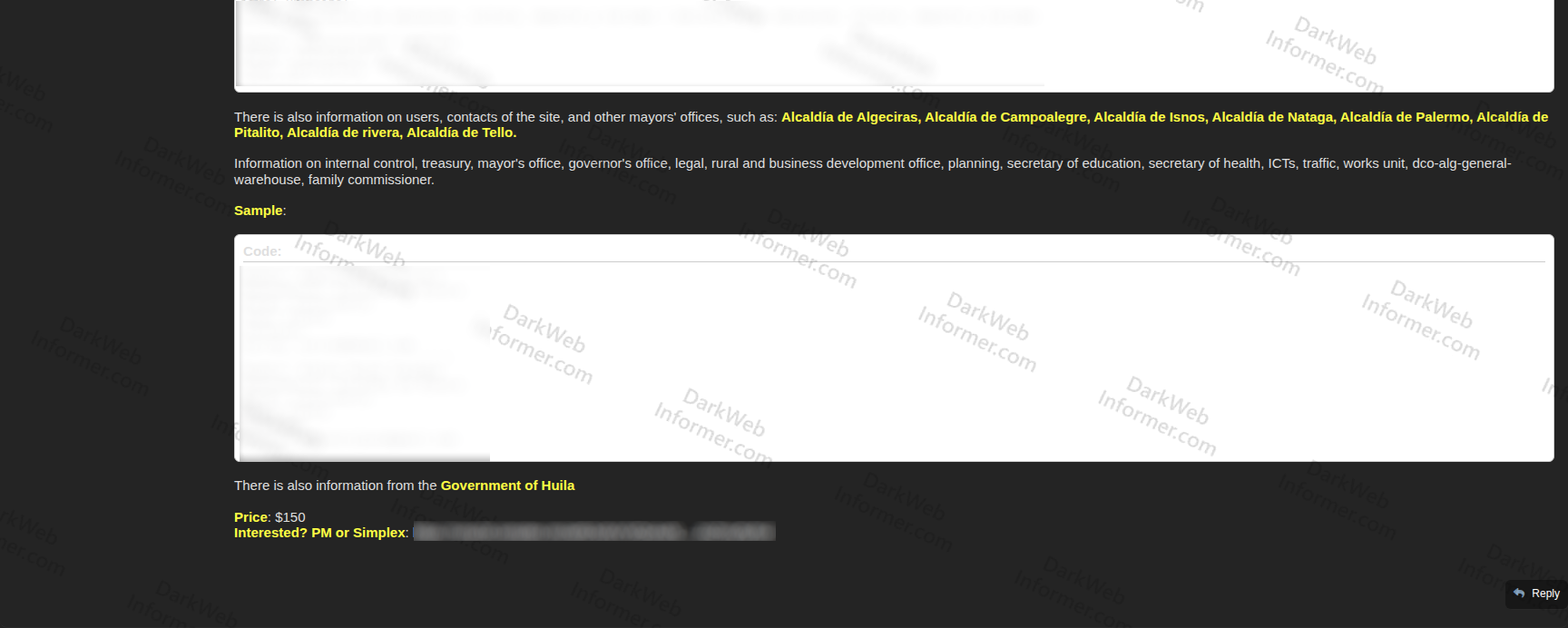
- Municipal Offices: User data, contacts, and site information for 8 mayors' offices (Alcaldias) across the Huila department: Algeciras, Campoalegre, Isnos, Nataga, Palermo, Pitalito, Rivera, and Tello.
The listing also references data from across 15+ government departments and offices including internal control, treasury, the governor's office, legal, rural and business development, planning, secretary of education, secretary of health, ICTs, traffic, works unit, dco-alg-general-warehouse, and the family commissioner. Additional information from the Government of Huila itself is also mentioned.
The data is priced at $150, with contact via PM or SimpleX messaging. The low price point and the collaborative nature of the listing (four named actors working together) suggest this is part of an organized campaign targeting Colombian government infrastructure. The fact that CryptoDead, who previously leaked the ICFES data affecting 30 million Colombians, is involved as a collaborator indicates a group with established interest in Colombian government targets.